- Should completely privileged and partially privileged documents be logged?
- What metadata fields must be included?
- Is a categorical privilege log allowed?
- Should the format be in Excel, PDF, or something else?
- When is the due date for the log? Will there be a log after every rolling production or one at the end?
- Are there sets of documents that should be excluded? For example, documents created after the date of the complaint or some other cut-off date, or documents that include particular outside counsel or specific topics.
Once these details have been confirmed, the following best practices should be implemented:
1. Organize the Population: Start with the Correct Review Set
The first step in creating a privilege log is ensuring you are working with the proper set of documents. A review team trying to determine privilege while logging will be inefficient and prone to inconsistencies, so logging documents should come after a thorough review where all privileged documents have been identified.
If logging both withheld and redacted documents, separating them into distinct search populations is best since reviewers will look for different things depending on whether a document is entirely withheld or redacted. Keeping them separate improves consistency and speeds up the logging process.
2. Think About the Outcome: What a Privilege Log Should Look Like
A privilege log should be clear, concise, and defensible. Here’s an example of a standard privilege log entry:
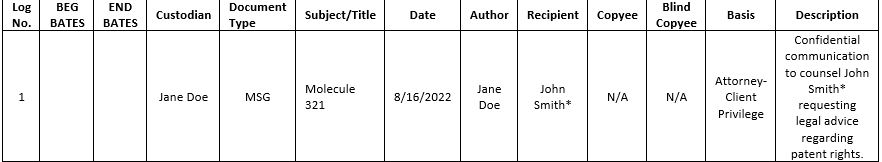
What makes this entry effective?
- The logline contains key metadata (Bates number, date, authors, recipients).
- There is a column that identifies the privilege basis (attorney-client privilege, work product).
- The description follows best practices (it describes the communication without revealing privileged details).
- An attorney has been clearly identified.
3. Ensure You Have the Necessary Metadata
Ensure you have all relevant metadata fields to create an accurate privilege log. For some of these, the metadata included in the review tool is sufficient.
- Date
- Document type/extension
- Subject line or file name, if available.
The Author(s) and recipient(s) fields (including CC and BCC) usually have to be normalized to remove extra content such as email addresses and brackets.
Additionally, attorneys should be identified using a consistent method, such as an asterisk (*) or “Esq.” designation. To avoid errors, it’s essential to cross-check attorney names against a reference list of known attorneys.
4. Draft Descriptions Efficiently with a Structured Workflow
A well-structured description should include:
- Document type (email, memorandum, notes).
- Who is providing or seeking legal advice (attorney-to-client, client-to-attorney).
- The general subject matter of the communication (without revealing privileged content).
To maintain consistency and efficiency, use predefined subject-matter categories such as:
- Contract negotiations
- Litigation strategy discussion
- Draft agreements
- Compliance issues
This process ensures descriptions are uniform but still specific.
5. Privilege type or basis
Finally, it’s essential to have a pick list for identifying the privilege basis or type. The two most common options fall under attorney-client privilege and the work product doctrine; however, other types of privilege, such as common interest privilege (also called the joint defense privilege), may come into play for certain matters.
6. Create a Glossary for Certainty on Attorney Identification
A common privilege logging issue is misidentifying attorneys or failing to distinguish them from non-attorney personnel. It’s also essential to catch third parties whose presence might mean that a given communication is not privileged. It’s important to note that not all parties break privilege.
The privilege log glossary, at a minimum, should include:
- All outside counsel attorneys involved in the matter.
- In-house counsel and their roles.
- Law firms and legal teams that are associated with the case.
- Experts or third parties who are part of legal consultations (if applicable).
Having an accurate Glossary of Names is vital because it prevents mistakes (for example, logging a document as privileged when the sender was not acting in a legal capacity).
It ensures consistency across the privilege log, reducing the risk of challenges from opposing counsel.
A well-structured privilege log is efficient, accurate, and defensible. By following these best practices—organizing the population, defining metadata, standardizing descriptions, and maintaining a privilege glossary—you ensure that privilege claims are upheld while minimizing challenges from opposing parties.